Social Engineering Examples
Social Engineering Examples - The 2025 printable calendar is a useful tool to keep your schedule organized in 2025. With various formats including monthly and yearly views, it offers flexibility for planning. Whether you're managing personal tasks or work schedules, this calendar keeps everything in order with simplicity and structure.
You can choose from a range of stylish and practical designs to suit your style. Simply get it and start using from the comfort of your home or office. A 2025 printable calendar is great for planning holidays, noting important events, and setting goals throughout 2025.
Social Engineering Examples
Social Engineering Examples
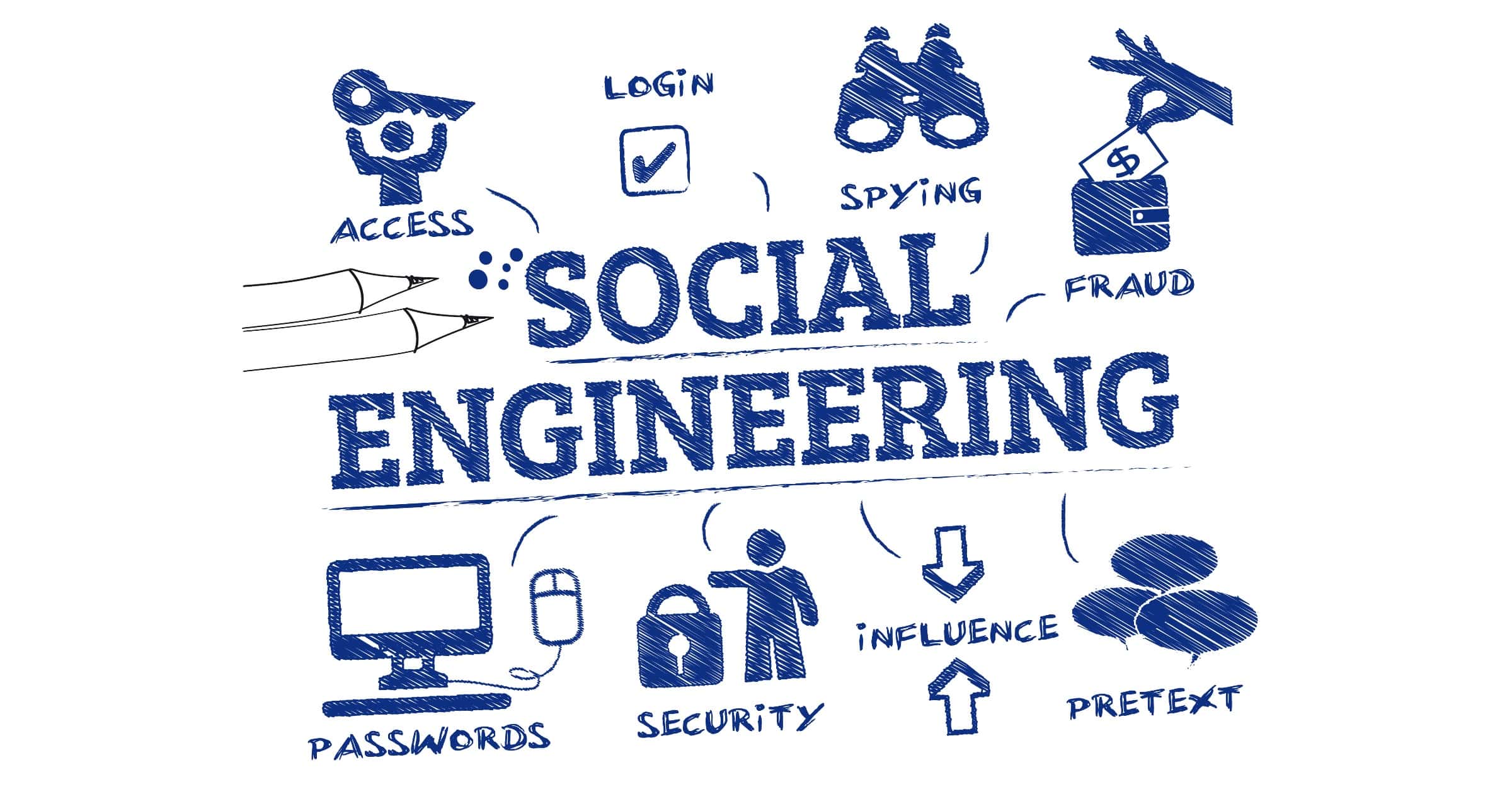
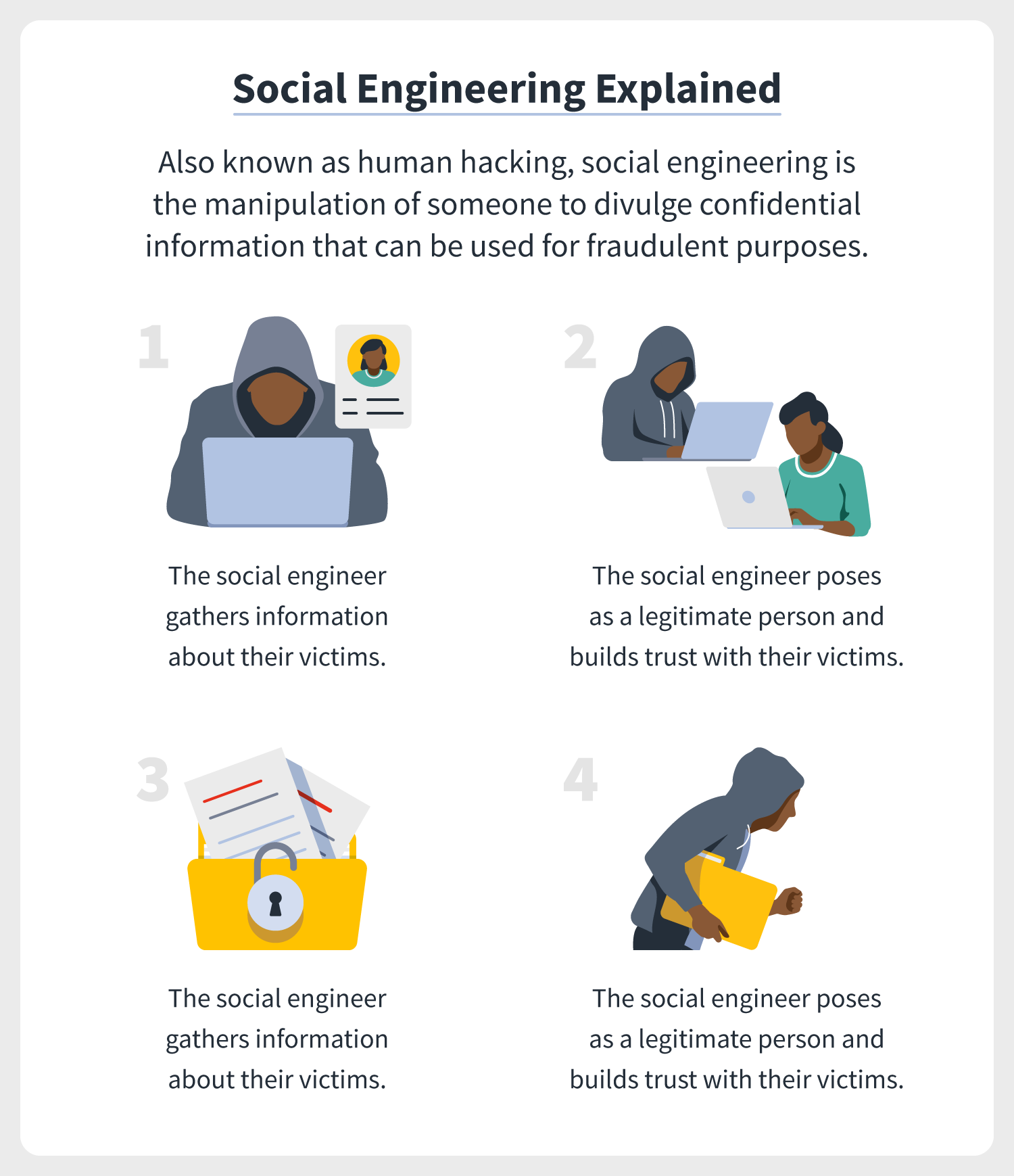
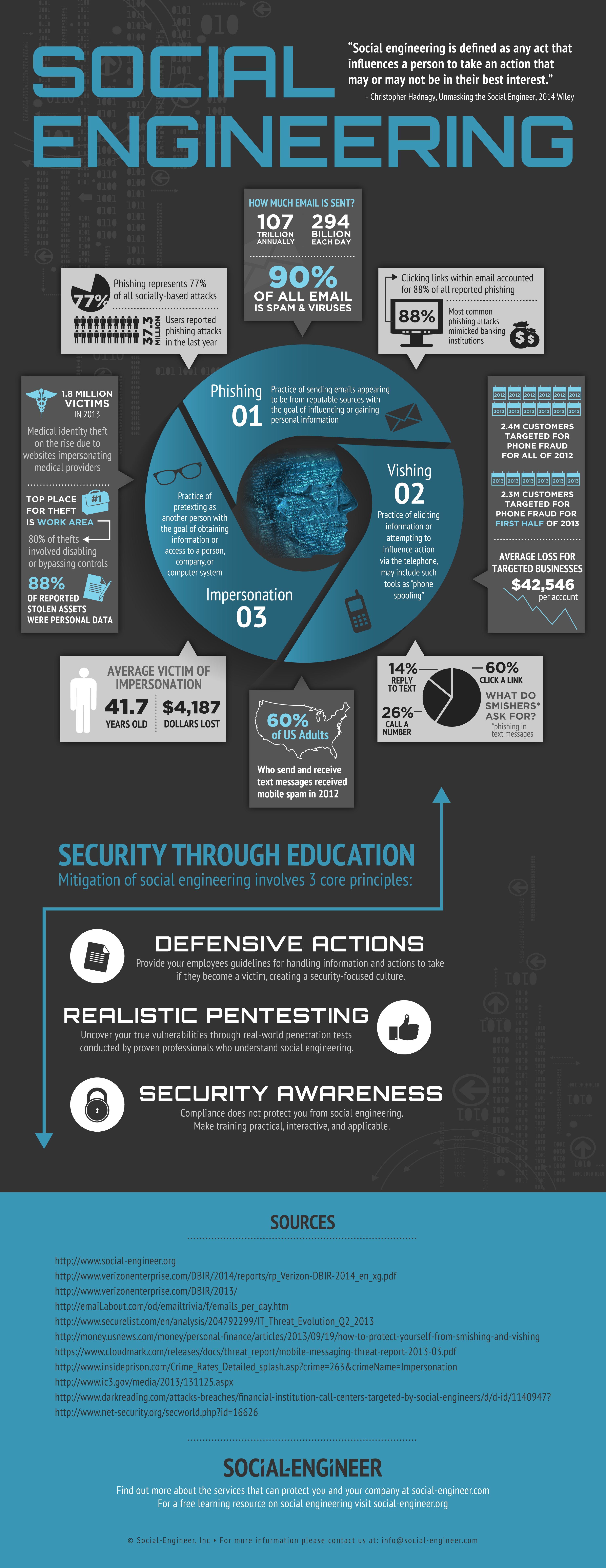
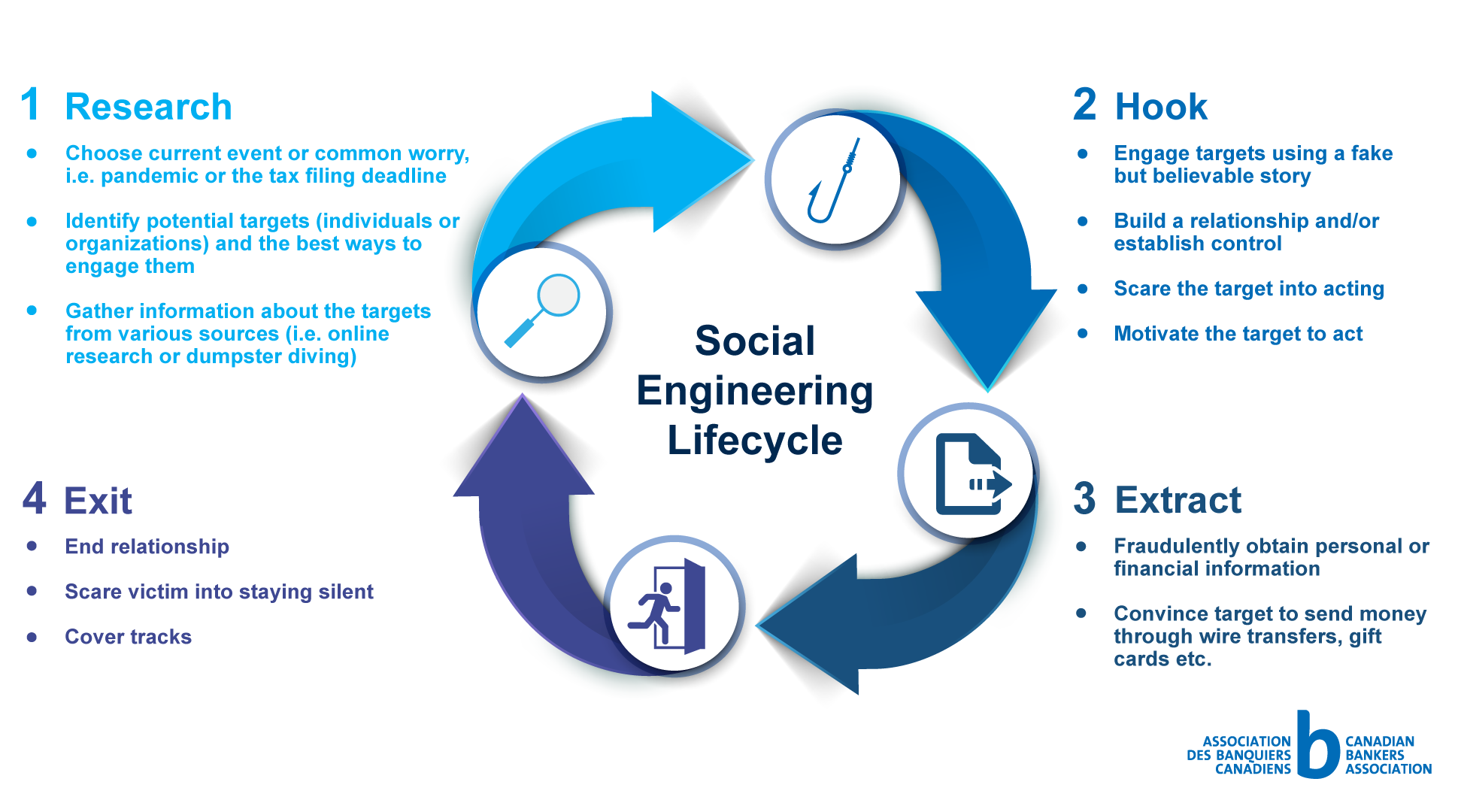
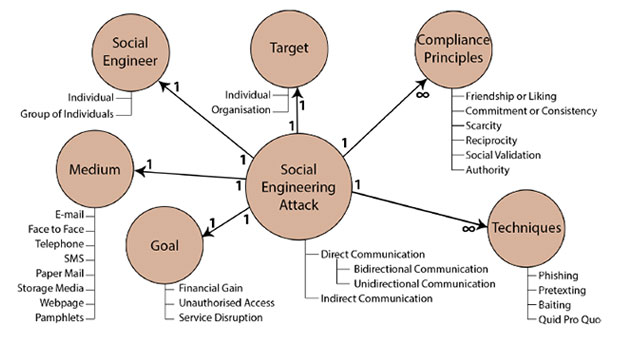
Web May 23 2023 nbsp 0183 32 Types of Social Engineering Attacks 1 Phishing A phishing attack is the most well known social engineering tactic A phishing attack uses an email website web ad web chat SMS or 2 Baiting 3 Quid Pro Quo 4 Pretexting 5 Tailgating ;An example: compromising a company’s cybersecurity measures to gain access to confidential customer records. In 2021, a record number of cybercrime complaints, largely a product of this kind of online scamming, complaints led to nearly $7 billion in losses .
What Is Social Engineering Definition Protection Tips Norton
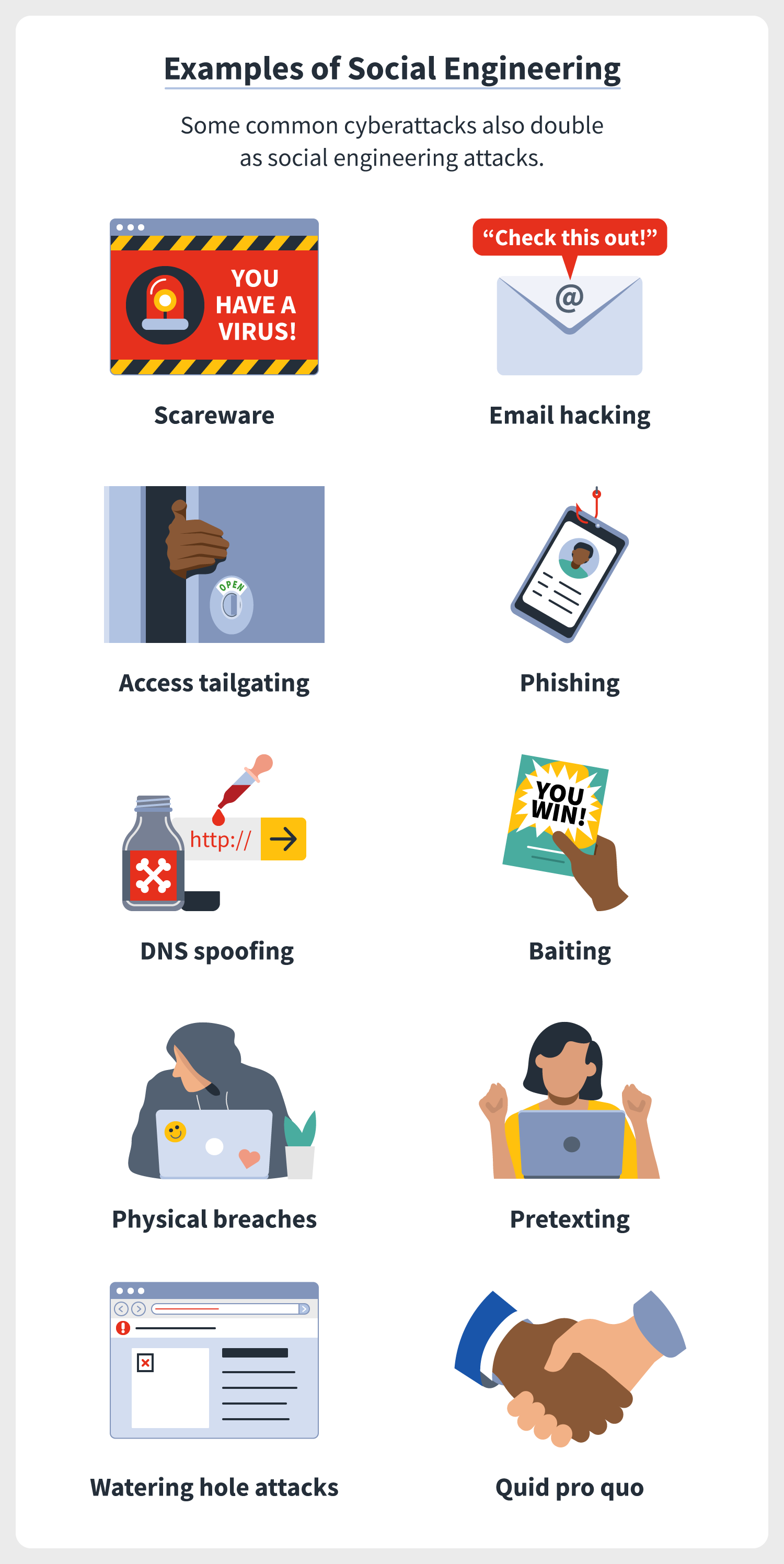
What Is Social Engineering
Social Engineering Examples;13 Examples of Social Engineering Techniques Common social engineering attacks include: Baiting A type of social engineering where an attacker leaves a physical device (like a USB) infected with a type of malware where it's most likely to be found. When a victim inserts the USB into their computer, a malware installation process … Web Feb 7 2022 nbsp 0183 32 Social engineering examples A good way to get a sense of what social engineering tactics you should look out for is to know about what s been used in the past
Key Takeaways. Social engineering is an illegal activity that accounts for 98% of cyber-attacks. Social engineering is characterized by attackers coercing victims into divulging sensitive information by pretending to be a known person or legitimate entity. Identity theft through phishing attacks is the most common form of social engineering. Social Engineering Examples In Hindi Free Learning Tech 3 Types Threats Of Social Engineering Imagineering Eau Claire WI
What Is Social Engineering How It Works amp Examples Built In
Is Social Engineering Illegal Capa Learning
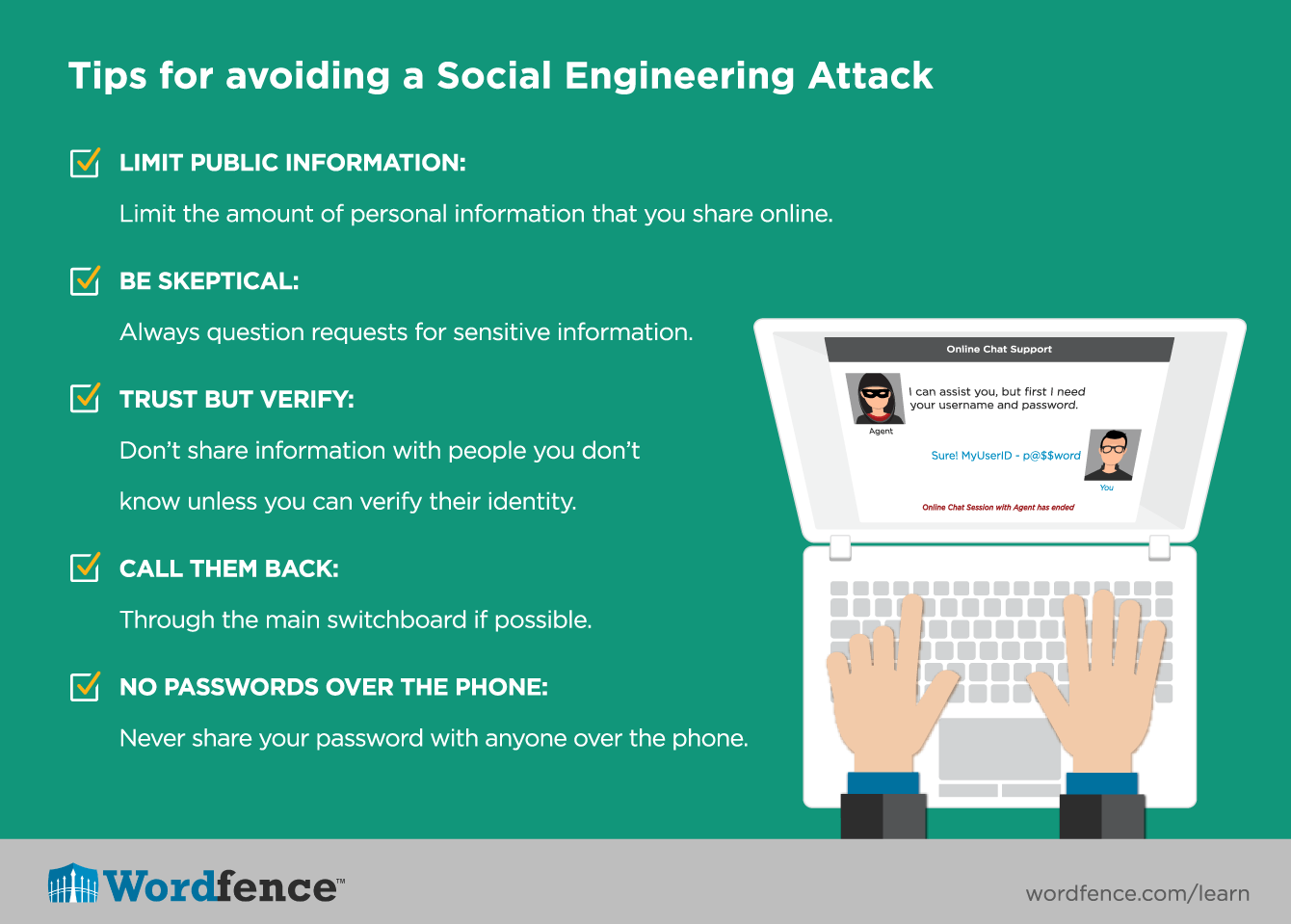
Web Examples of useful procedures to include are Password management Guidelines such as the number and type of characters that each password must include how often a password must be changed and even a simple rule that employees should not disclose passwords to anyone regardless of their position will help secure information assets Social Engineering Attacks A Look At Social Engineering Examples In Action Hashed Out By The
Web What is social engineering Phishing Phishing attacks are digital or voice messages that try to manipulate recipients into sharing sensitive information downloading malicious Baiting Tailgating Pretexting Quid pro quo UK Computer Emergency Response Team CERT Introduction To Social Engineering Public Intelligence What Is Social Engineering Definition
Social Engineering Infographic Realsocialengineering
How To Identify And Avoid Social Engineering Cyber Attacks How To Identify And Avoid Social
Setting Up Roadblocks To Social Engineering Cybersecurity Eloti Designs

15 Examples Of Real Social Engineering Attacks Updated 2022 2022
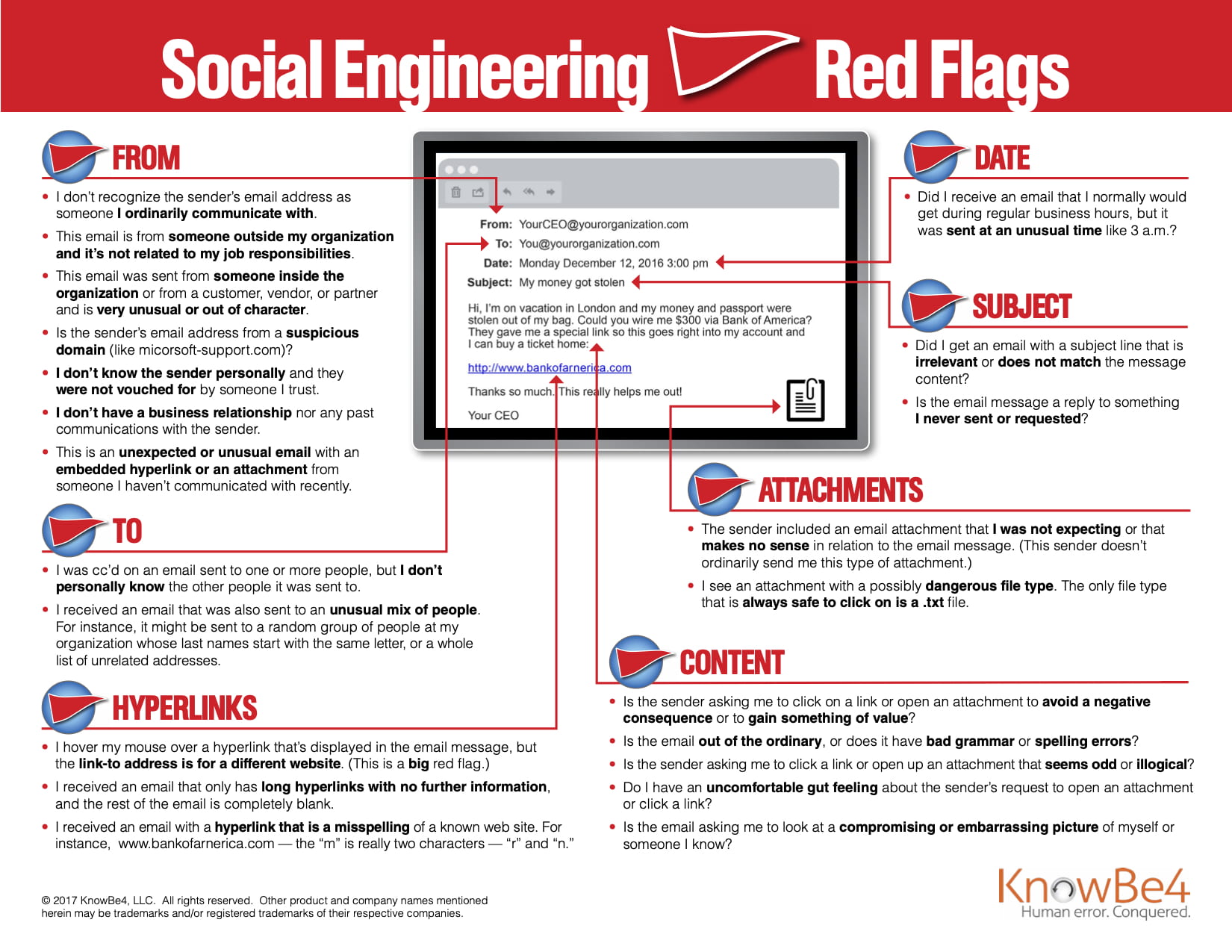
INFOGRAPHIC 22 Social Engineering Red Flags Office Of Information Security Washington
Understanding Social Engineering Techniques

The Growing Threat Of Social Engineering Is Your Team Equipped

Social Engineering Attacks A Look At Social Engineering Examples In Action Hashed Out By The

Job Ad Design Social Media Job Ads Social Media Computer Science

Social Engineering Examples Evolutionary IT