What Is Buffer Overflow Attack
What Is Buffer Overflow Attack - The calendar for 2025 is a handy tool to keep your schedule organized throughout the year. With layouts like monthly, yearly, and weekly formats, it offers versatility for planning. Whether you're organizing life or business tasks, this calendar keeps everything in order with clarity and ease.
You can choose from a range of clean and customizable layouts to suit your needs. Simply access and print from the comfort of your home or office. A 2025 printable calendar is great for planning holidays, marking appointments, and staying productive all year long.
What Is Buffer Overflow Attack

What Is Buffer Overflow Attack
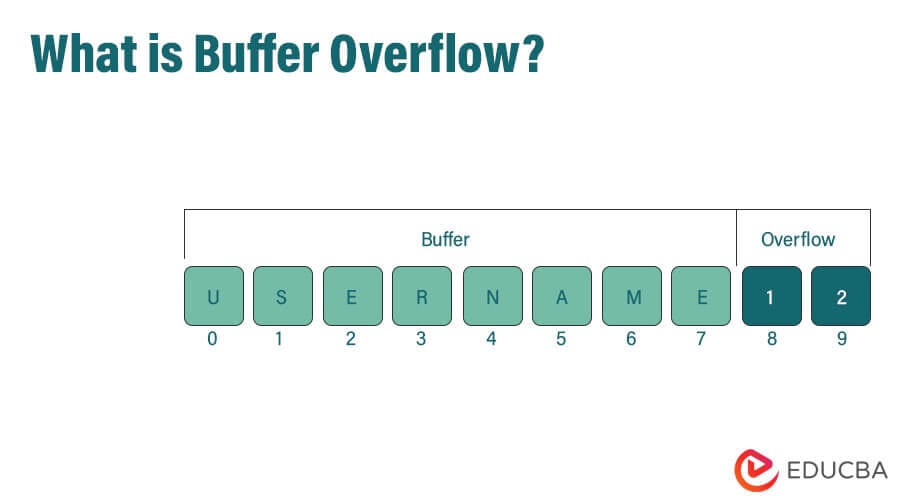
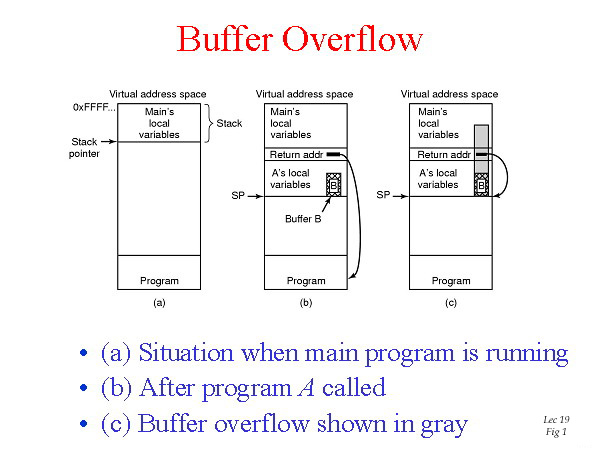
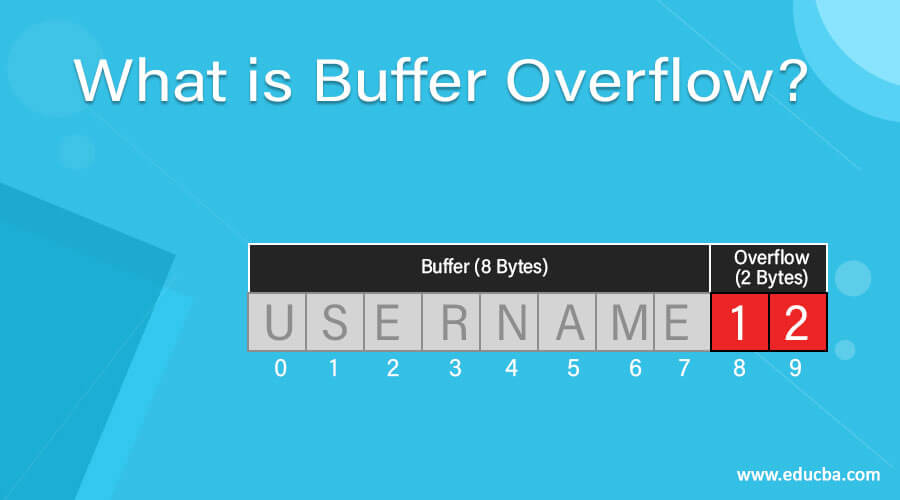
A buffer overflow occurs when the size of information written to a memory location exceeds what it was allocated This can cause data corruption program crashes or even the execution of malicious code While C C and Objective C are the main languages which have buffer overflow vulnerabilities as they deal Buffer overflow is a common type of cyber attack that can have serious consequences for individuals and organizations. It occurs when a computer program attempts to write more data to a buffer (a temporary storage area) than it can hold, resulting in data written to adjacent memory locations.
What Is A Buffer Overflow How Do These Types Of Attacks

What Is A Buffer Overflow Attack Types Examples
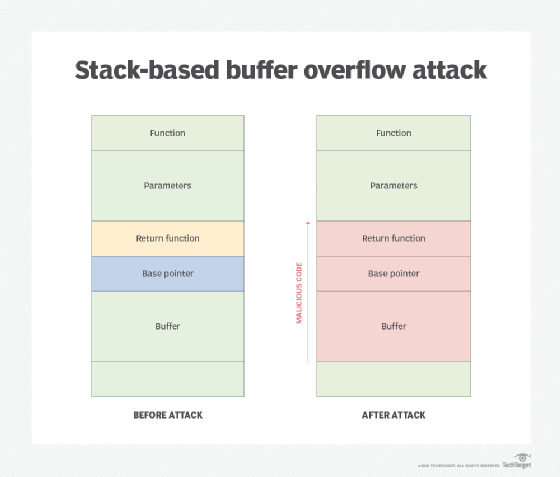
What Is Buffer Overflow AttackAttackers use buffer overflows to corrupt the execution stack of a application. By sending carefully crafted input to a application, an attacker can cause the application to execute arbitrary code – effectively taking over the machine. What is a Buffer Overflow Attack Attackers exploit buffer overflow issues by overwriting the memory of an application This changes the execution path of the program triggering a response that damages files or exposes private information
A buffer overflow attack can be: Stack-based. Your attacker sends data to a program, and that transmission is stored in a too-small stack buffer. Your hacker could choose a "push" function and store new items on the top of the stack. Or the hacker could choose a "pop" function and remove the top item and replace it. What Is Buffer Overflow Attack Hirehacker Contact 917508366000 What Is The Best Way To Remove The Vulnerability Caused By Buffer
What Is Buffer Overflow Prevention And Types Of Buffer
How Do Buffer Overflow Attacks Work
Buffer overflows typically have a high severity ranking because they can lead to unauthorized code execution in cases where attackers can control the overwritten memory space outside the Buffer Overflows Made Easy Thanks The Cyber Mentor Hack Sudo
Buffer overflow is an anomaly that occurs when software writing data to a buffer overflows the buffer s capacity resulting in adjacent memory locations being overwritten In other words too much information is being passed into a container that does not have enough space and that information ends up replacing data in adjacent PPT A Buffer Overflow Example PowerPoint Presentation Free Download Buffer Overflow Attack CyberHoot
What Is Buffer Overflow Attacks Solutions Preventions

What Is A Buffer Overflow Acunetix
Prevent Buffer Overflow Attack Backtrack Linux Tutorial

Figure 1 From The Buffer Overflow Attack And How To Solve Buffer
Upload A File To Commit A Buffer Overflow Attack Knight Jece1939
What Is Buffer Overflow A Comprehensive Guide CYBERVIE

Buffer Overflow Attack Tutorial 0x00 YouTube

Buffer Overflows Made Easy Thanks The Cyber Mentor Hack Sudo
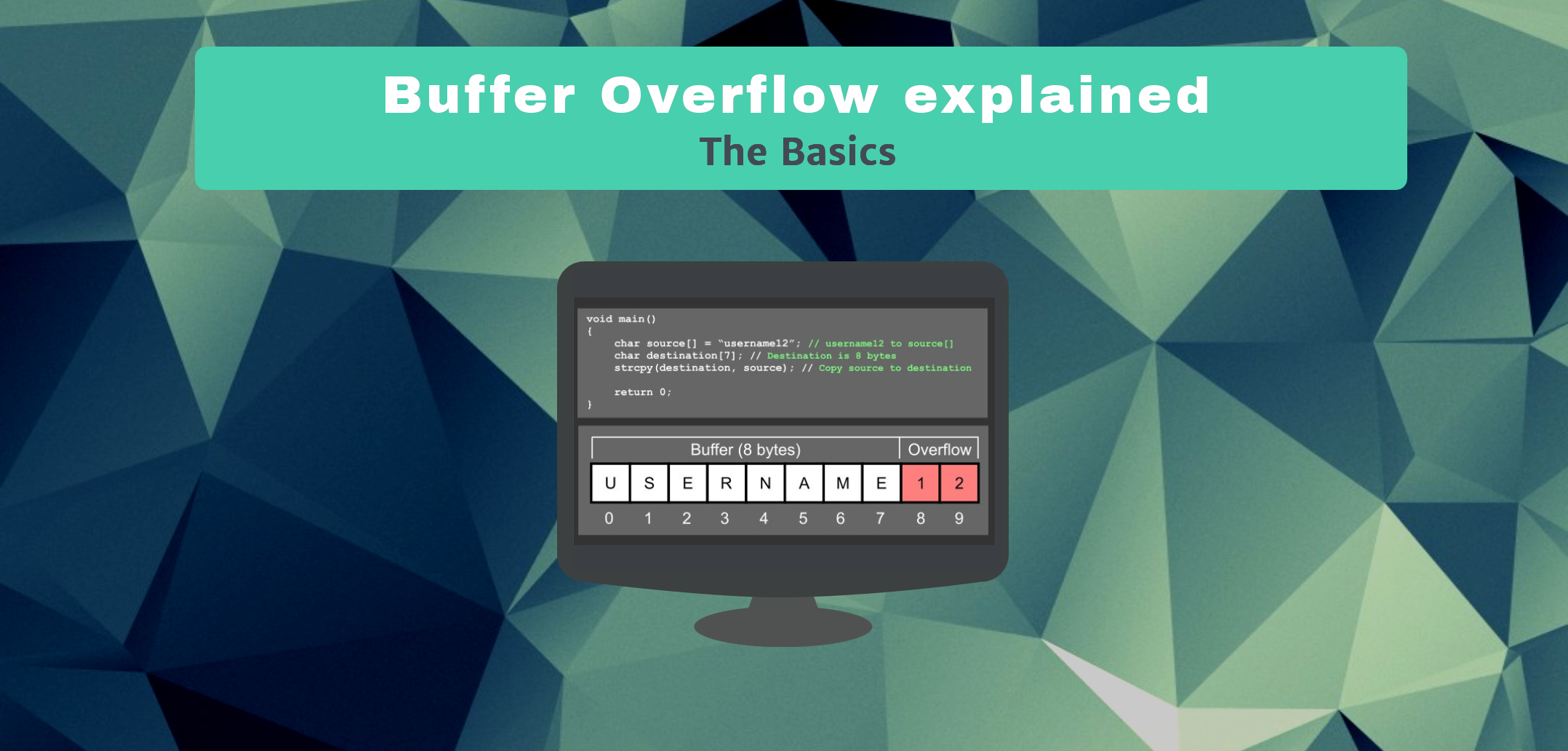
Buffer Overflow Explained The Basics Hacking Tutorials
Understanding Buffer overflow Please Support My Articles By Clicking