Information Security Risk Assessment Process
Information Security Risk Assessment Process - The 2025 printable calendar is a essential tool to stay on top of plans in 2025. With various formats including monthly and yearly views, it offers convenience for planning. Whether you're organizing life or professional deadlines, this calendar keeps everything in order with clarity and ease.
You can choose from a range of stylish and practical designs to suit your style. Simply access and print from the comfort of your home or office. A 2025 printable calendar is perfect for tracking vacations, marking appointments, and managing priorities all year long.
Information Security Risk Assessment Process

Information Security Risk Assessment Process
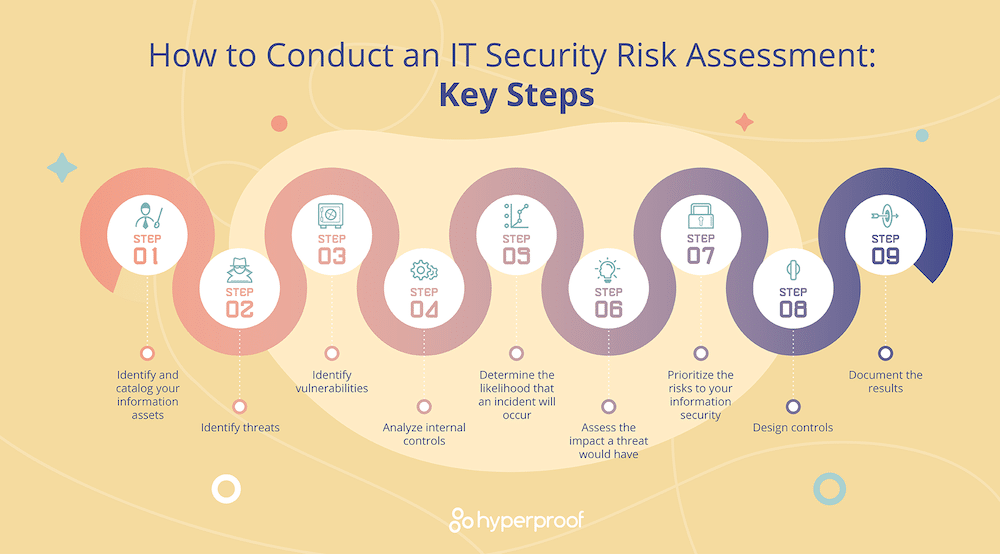
Web May 18 2022 nbsp 0183 32 Performing an Information Security and Privacy Risk Assessment Attributes of Information Security and Privacy Structure Structure evaluates the controls that address the structural Security and Privacy Measures There is a need for security and privacy measures and to establish the control ;1. Define your risk assessment methodology There is no set ISO 27001 risk assessment procedure. Instead, you should tailor your approach to the needs of your organisation. To do this, you need to review certain things. First, you should look at your organisation’s context.
Guide For Conducting Risk Assessments NIST

Information Security Risk Assessment Integrates Risk Management Activities Into The Enterprise
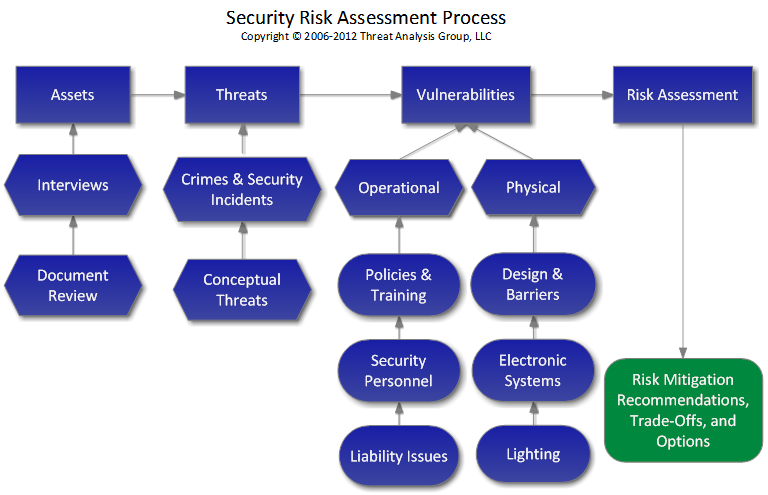
Information Security Risk Assessment ProcessThe 4 steps of a successful security risk assessment model Identification. Determine all critical assets of the technology infrastructure. Next, diagnose sensitive data that is... Assessment. Administer an approach to assess the identified security risks for critical assets. After careful ... Web How to perform a cybersecurity risk assessment in 5 steps Step 1 Determine the scope of the risk assessment A risk assessment starts by deciding what is in scope of the Step 2 How to identify cybersecurity risks You can t protect what you don t know so the next task is to identify and
A risk assessment involves: Identifying threats and vulnerabilities that could adversely affect the data, systems or operations of UCI. Evaluating current security practices against the requirements in the UCI Information Security Standard (ISS). Creating action plans to remediate prioritized risks identified in the risk assessment questionnaire. Information Security Risk Assessment Template Beautiful It Security Risk Assessment Template Security Risk Assessment Template Elegant 7 Security Assessment Samples Examples Templates
ISO 27001 Risk Assessment 7 Step Guide IT Governance UK Blog

Custom Essay Amazonia fiocruz br
Web A security risk assessment identifies security risks in a computing system evaluates and prioritizes those risks and suggests security controls that can mitigate the risks Another aspect of security risk assessments is vulnerability assessment the process of identifying and remediating vulnerabilities across the organization How To Buy A Cybersecurity Risk Assessment That Meets Your Objectives
Web Risk assessment is a process during which an organization should identify information security risks and determine their likelihood and impact Plainly speaking the organization should recognize all the potential problems with their information how likely they are to occur and what the consequences might be Introducing Information Security Risk Assessment Process Workflow Ppt Portfolio Presentation What Are The 5 Key Steps To Doing A Risk Assessment Crashtheteaparty

Tips For Effective Crisis Management Event Strategies For Success
800 30 Risk Assessment Spreadsheet Securing Electronic Health Records On Mobile Devices Pdf
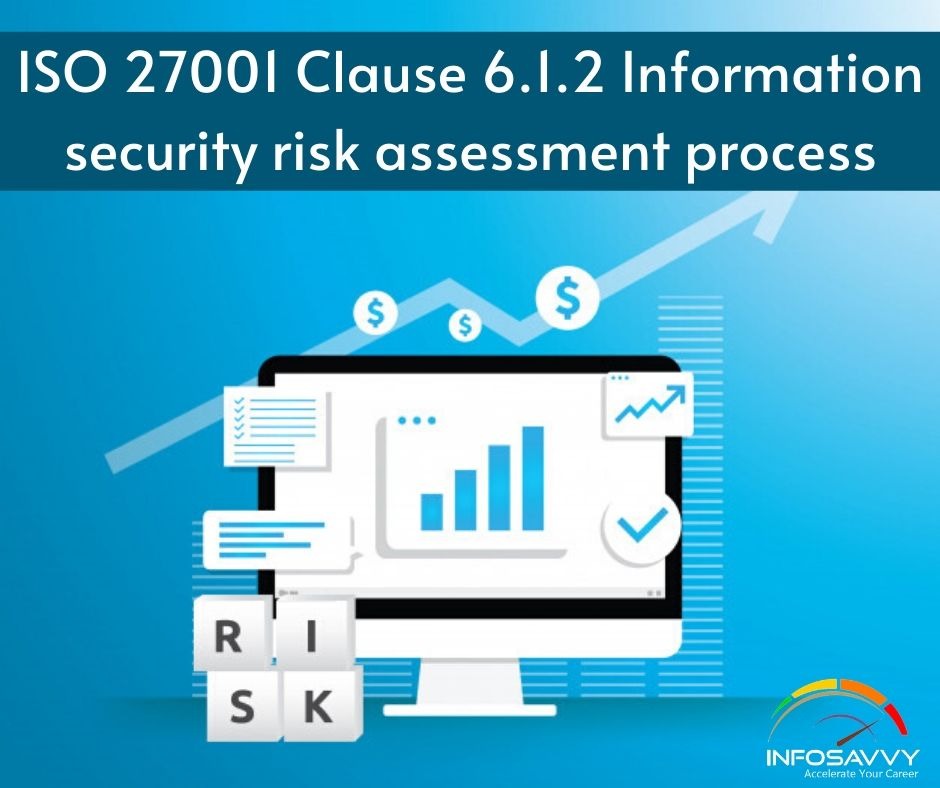
ISO 27001 Clause 6 1 2 Information Security Risk Assessment Process Infosavvy Security And IT
![]()
Security Risk Assessment Intelligent Avatar

Information Security Risk Management Process Download Scientific Diagram
SECURITY RISK MANAGEMENT INDEPENDENT SECURITY CONSULTANTS

Information Security Risk Assessment Process Ppt Powerpoint Presentation Shapes Cpb PowerPoint

How To Buy A Cybersecurity Risk Assessment That Meets Your Objectives

Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment

PDF Introducing Octave Allegro Improving The Information Security Risk Assessment Process